La versión 2021 del Top 10 de vulnerabilidades en aplicaciones web de OWASP ha sido liberada oficialmente.
Esta lista de vulnerabilidades es una referencia clave en la industria de seguridad informática y conlleva una actualización que es importante que conozcamos quienes estamos involucrados en ella.
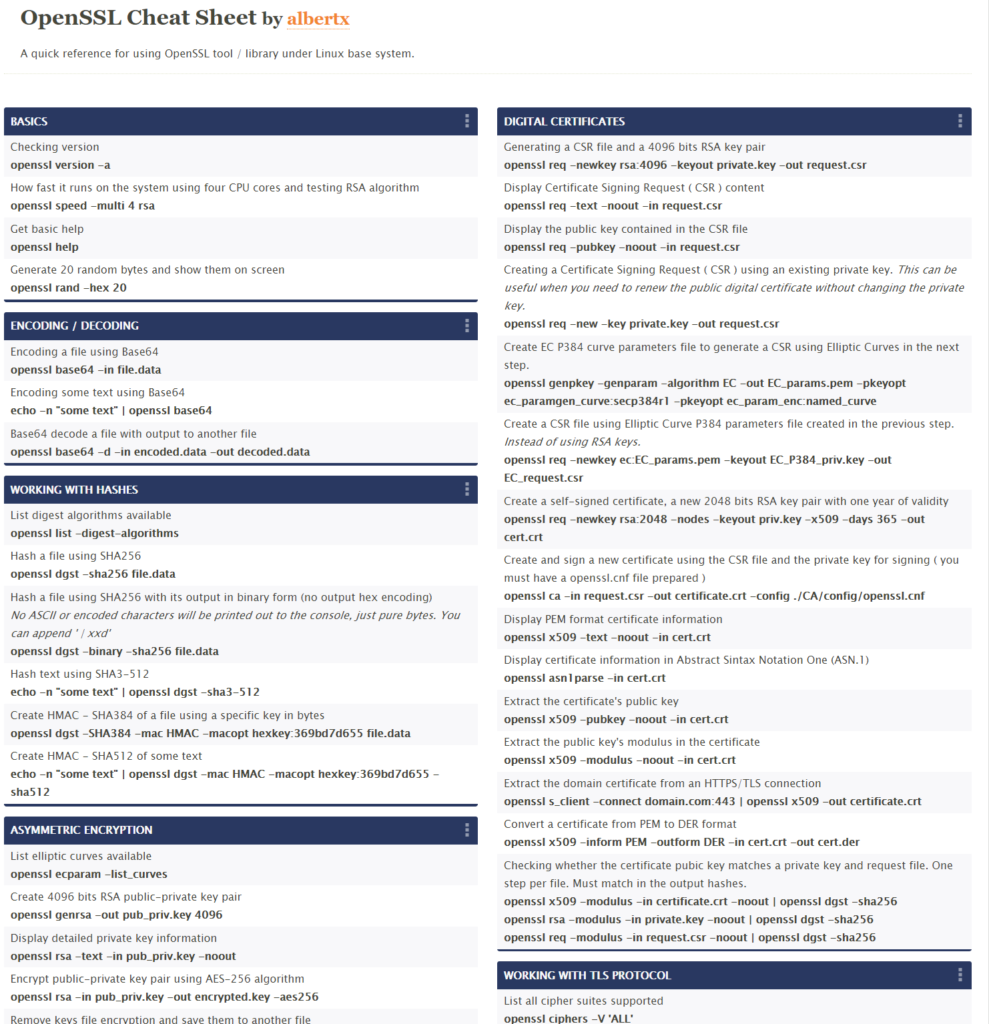
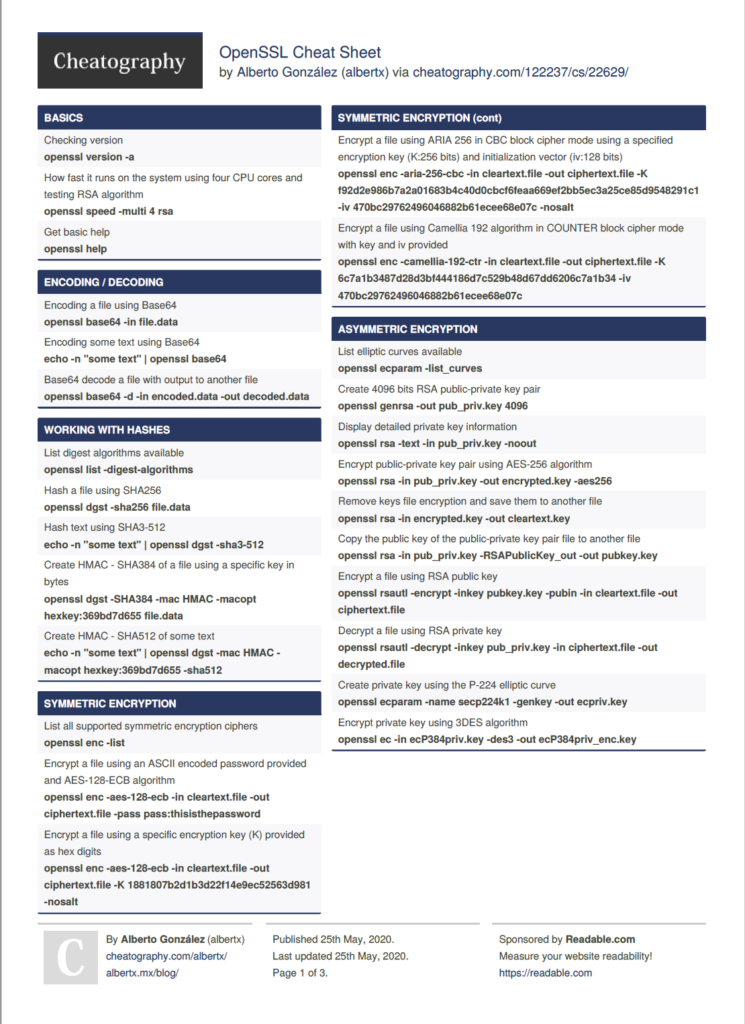
Particularmente una de las cosas que llama la atención es la inclusión de una categoría denominada A02: Cryptographic Failures. Esta categoría incluye los debilidades ( CWE ) asociadas a fallas criptográficas ya sea por problemas en las configuraciones o en las implementaciones de la criptografía en las aplicaciones. Entre ellas destacan:
- Debilidad en las contraseñas.
- Intercambio de llaves criptográficas sin autenticación.
- Nivel de entropía insuficiente.
- Problemas en la generación de datos pseudoaleatorios.
- Transmisión de información sensible en claro.
- entre muchos otros.
… seguramente estaré platicando de algunas en el transcurso de los días.
La lista actualizada de vulnerabilidades quedó de la siguiente forma:
- A01:2021-Broken Access Control
- A02:2021-Cryptographic Failures
- A03:2021-Injection
- A04:2021-Insecure Design
- A05:2021-Security Misconfiguration
- A06:2021-Vulnerable and Outdated Components
- A07:2021-Identification and Authentication Failures
- A08:2021-Software and Data Integrity Failures
- A09:2021-Security Logging and Monitoring Failures
- A10:2021-Server-Side Request Forgery
El enlace oficial y toda la documentación la encuentran directamente en el portal de OWASP.org Top 10.